Essential Security Steps for Your New Windows PC: A Q&A Guide
Many years ago, when I'd get my hands on a new Windows PC, I did what a lot of people do. I opened the browser, signed in to a few accounts, changed my desktop wallpaper, and installed a few apps. It felt ready within minutes. Then I stopped to check the security settings and realized almost none of the important stuff had been left half configured. I don't do that anymore. Now I follow a strict set of steps to lock down the system from day one. Below are answers to the most common questions about my approach, covering everything from Windows Defender to startup management.
Why did the author change their approach to setting up a new Windows PC?
The author realized that their quick-start routine—opening a browser, signing into accounts, changing the wallpaper, and installing apps—left critical security settings half-configured. After years of neglecting the security configuration, they discovered that the default settings of Windows often leave gaps exploitable by malware or unauthorized access. The turning point came when they took a moment to actually review the security dashboard and found that Windows Defender was not fully enabled, User Account Control (UAC) was set too low, and disk encryption was off. This experience taught them that a new PC is most vulnerable right out of the box, and a few minutes of deliberate setup can prevent hours of cleanup later. Now, instead of focusing on personalization, they prioritize tightening security before connecting to the internet or entering any credentials.
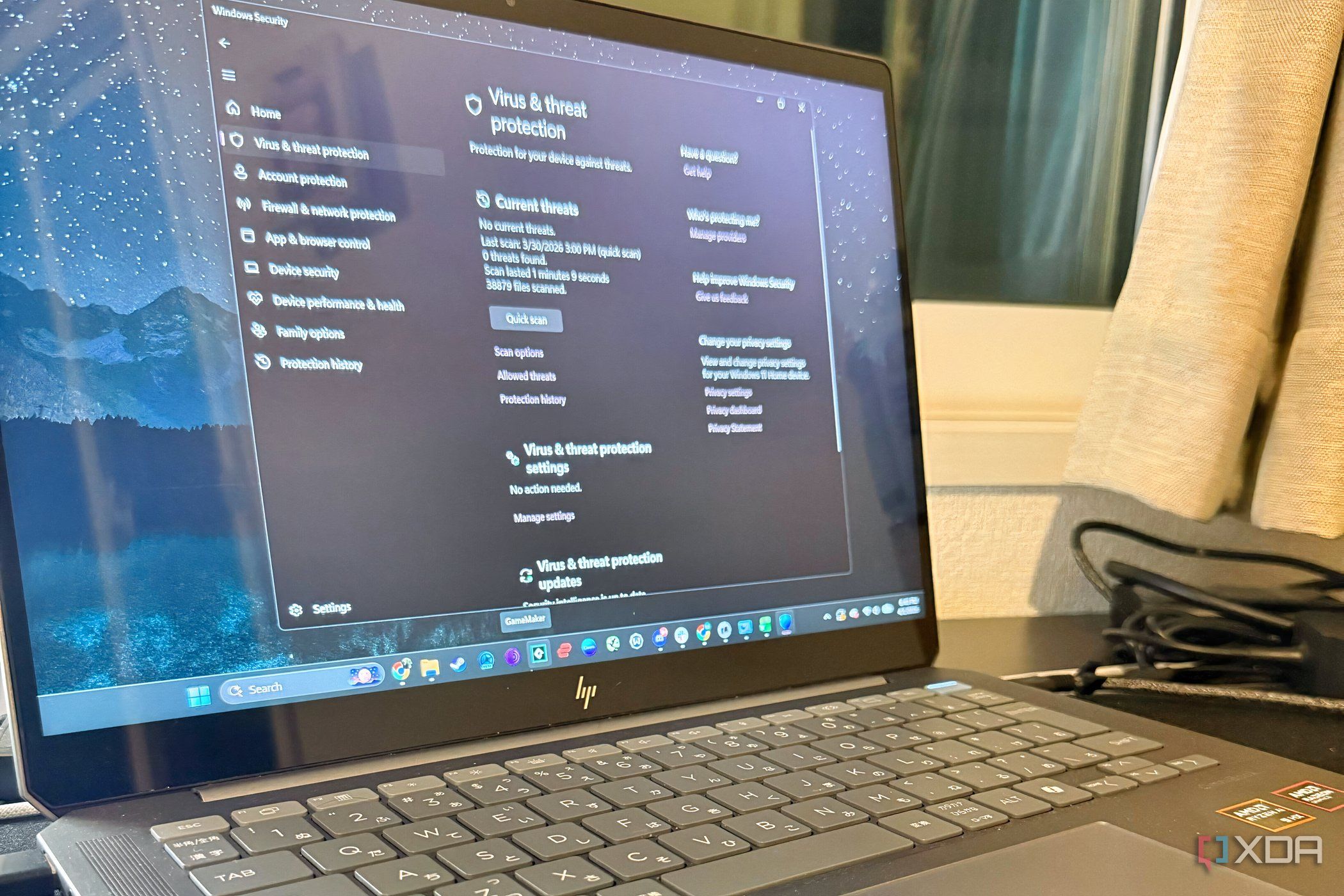
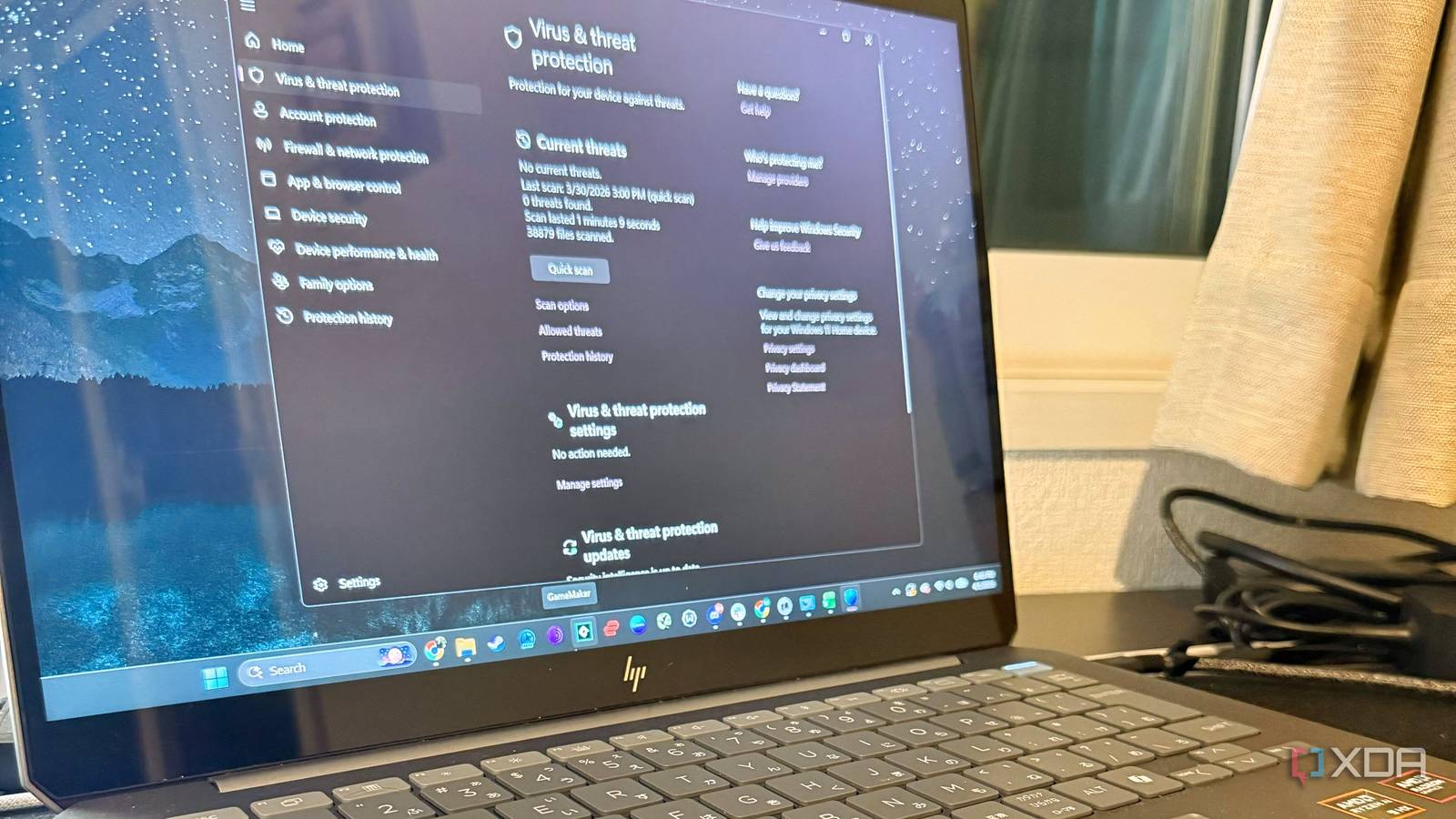
What is the first security step the author takes on a new Windows PC?
The first step is to ensure Windows Security (formerly Windows Defender) is fully active and updated. This includes checking that real-time protection, cloud-delivered protection, and automatic sample submission are all turned on. The author navigates to Settings > Update & Security > Windows Security > Virus & threat protection and verifies that no third-party antivirus has been pre-installed that might conflict. They also run a quick scan to confirm the engine is working. Many new PCs ship with trial versions of other security software that can disable Windows Defender, so removing those trials and relying on Microsoft’s built-in solution is a key early move. This step alone catches most common threats and provides a solid baseline before installing any other software.
How does the author protect data with BitLocker encryption?
After securing the antivirus, the author enables BitLocker drive encryption on the system drive. BitLocker uses AES encryption to protect all data in case the laptop is lost or stolen. They go to Control Panel > System and Security > BitLocker Drive Encryption and turn it on for the C: drive. If the PC lacks a TPM chip (common in older models), they configure BitLocker to use a startup key saved on a USB drive or a password. The author emphasizes saving the recovery key to a Microsoft account or printing it out—never storing it on the encrypted drive itself. This step adds a layer of physical security that prevents offline attacks, and it takes only a few minutes but can save years of regret if the device falls into the wrong hands.
What User Account Control settings does the author adjust and why?
The author raises User Account Control (UAC) to the second-highest level—“Always notify me when apps try to install software or make changes to my computer.” To do this, they search for “UAC” in the Start menu and drag the slider up. While some users find the constant prompts annoying, the author considers it a critical early-warning system. Many malware infections start by silently modifying system settings; with UAC maxed out, any such attempt triggers a pop-up that can be denied. The author also notes that this setting does not interfere with normal workflows once trusted software is allowed through. It’s a small inconvenience for a significant boost in preventing unauthorized administrative actions.
How does the author manage startup programs and services to reduce the attack surface?
The final step is trimming startup programs and disabling unnecessary services. The author opens Task Manager (Ctrl+Shift+Esc) and goes to the Startup tab, then disables any item that is not essential—especially third-party updaters, cloud sync apps, and pre-installed bloatware. They also run services.msc and set services like Remote Registry, Windows Remote Management, and Print Spooler (if no printer is used) to “Disabled.” This reduces the number of processes that can be exploited. The author recommends researching each service before disabling, but common sense wins: if you don’t use remote desktop, turn off Remote Desktop Services. This cleanup not only boosts performance but also closes potential entry points for attackers lurking in seldom-used services.
Related Articles
- Security Experts Reveal: Old Android Phones Outperform Cheap IP Cameras in New Surveillance Trend
- Silver Fox Unleashes New 'ABCDoor' Backdoor in Tax-Themed Phishing Waves Against Russia and India
- German Police Unveil Real Name and Face of Notorious Russian Ransomware Kingpin 'UNKN'
- SentinelOne Warns: AI-Powered Attacks Require AI-Native Defense at Machine Speed
- Germany Reclaims Top Spot in European Cyber Extortion Surge
- The Ultimate Guide to Launching a Career as a Cybersecurity Consultant
- AI-Driven Vulnerability Discovery: How Enterprises Can Adapt to a Faster Threat Landscape
- How to Effectively Respond to a Source Code Repository Breach: A Step-by-Step Guide Inspired by the Trellix Incident