Frontier AI Sparks Race in Cyber Defense: SentinelOne Reveals How Machine-Speed Autonomy Stops Zero-Day Threats
In a move that underscores the accelerating cyber arms race, OpenAI and Anthropic have unveiled new frontier AI capabilities—but SentinelOne warns the real breakthrough lies not in raw model power but in machine-speed autonomous defense. The cybersecurity firm, which has worked closely with these labs for years, claims that only AI-native systems can keep pace with both malicious and benign uses of advanced models.
“The latest announcements from OpenAI and Anthropic reinforce what we’ve believed for years: the future of cybersecurity will be shaped by AI-native defense,” said Ric Smith, CTO of SentinelOne. “Our partnerships provide meaningful insight into how advanced models evolve—and where they create real impact across security.” Many of these learnings are already embedded in SentinelOne’s platform, stopping zero-day exploits daily that no other solution can block.
Background: The Frontier AI Revolution in Security
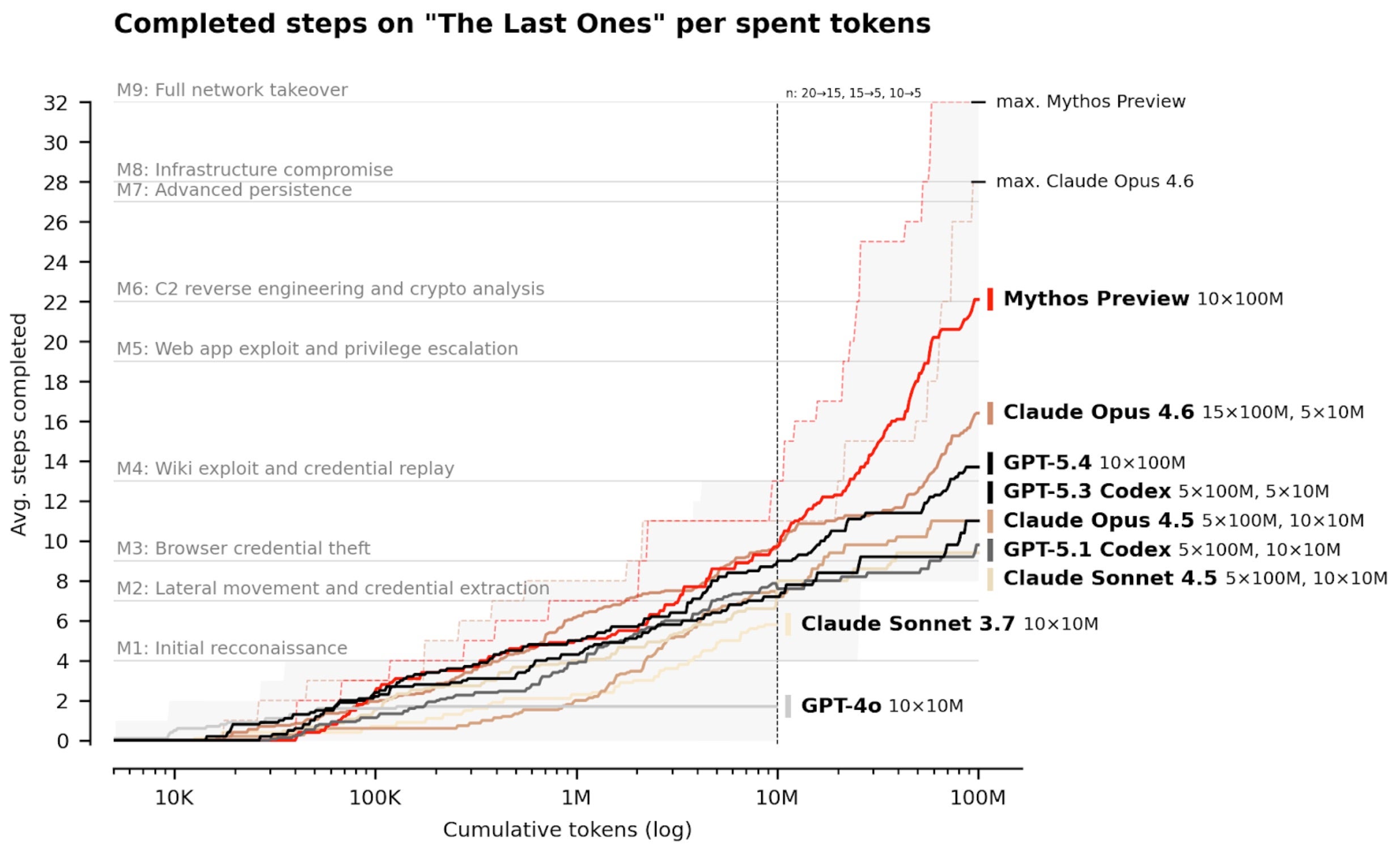
Frontier models—from GPT-4o to Claude 3.5—are rapidly improving how defenders identify weaknesses, analyze complex systems, and reason about attack paths at scale. However, they also give attackers the advantage of speed and scale when finding new vulnerabilities. SentinelOne emphasizes that progress in this race matters, but it is only part of the broader picture.
“Raw vulnerability counts rarely map cleanly to real-world risk,” Smith added. “Many vulnerabilities are not meaningfully exploitable in live environments, and many are already reduced by architectural layers, controls, and runtime protections.” The gap between theoretical exposure and operational risk is substantial; what matters is the ability to understand real conditions, prioritize, and stop actual attacks.
What This Means: Speed and Autonomy Become Critical
The implications are clear: cybersecurity must operate at machine speed. SentinelOne was built from day one using behavioral AI, automation, and autonomous protection to detect, defend, and respond across endpoint, cloud, identity, data, network, and AI attack surfaces. As frontier AI advances, the value of this approach only grows.
Recent attacks illustrate the point. In the last few weeks alone, supply chain attacks like LiteLLM, Axios, and CPU-Z exploited novel threats and zero-day vulnerabilities. In each case, autonomous response at machine speed was the only antidote. “We’ve demonstrably expanded our own ongoing efforts to ensure our platform stops these threats,” Smith noted. “No other solution can currently block them.”
The company also pointed to its long-standing collaboration with Google DeepMind, which has provided critical insights into how frontier models evolve and where they can create security impact. These capabilities are already embedded in existing products, protecting customers from the most advanced attacks.
For the broader industry, the message is urgent: the race between attackers and defenders is now defined by AI speed. Organizations that fail to adopt autonomous, AI-native defenses risk falling behind. As frontier models become more capable, the ability to respond in real-time—not just detect—will separate the secure from the compromised.
Learn more about the frontier AI shift | Understand the implications for your organization
Related Articles
- 5 Crucial Insights on OpenAI’s Hypocrisy: Restricting Cyber After Slamming Anthropic’s Mythos Limits
- A Complete Guide to Fortifying Your LLM Against Prompt Injection with StruQ and SecAlign
- 7 Critical Facts About Ubuntu 16.04 LTS: Security Support Has Ended
- A Practical Guide to Understanding and Defending Against Nation-State Wiper Attacks: The Stryker Case Study
- How to Uncover Security Flaws with AI: Lessons from the Firefox Zero-Day Discovery
- Microsoft Shatters Record with 167 Patches in April 2026 Update, Including Actively Exploited Zero-Days
- Iran-Targeted Wiper Worm 'CanisterWorm' Strikes Cloud Systems in Cybercrime Escalation
- Understanding the Supply-Chain Attacks on Checkmarx and Bitwarden: A Step-by-Step Breakdown